The IIS Chip Gallery
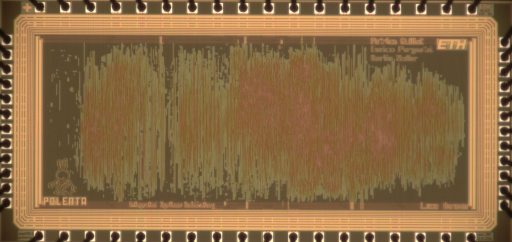
Polenta (2009)
by
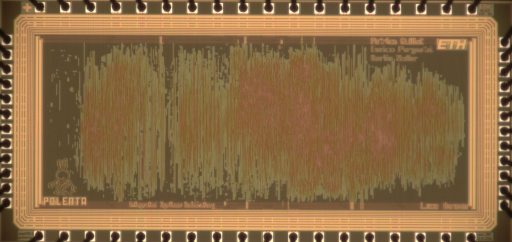
| Application | Cryptography |
| Technology | 180 |
| Manufacturer | UMC |
| Type | Semester Thesis |
| Package | QFN56 |
| Dimensions | 3840μm x 1525μm |
| Gates | 160 kGE |
| Voltage | 1.8 V |
| Power | 110 mW |
| Clock | 142.2 MHz |
As a result of the encountered weaknesses of the widely used SHA-1 hash algorithm, and due to concerns on the similarly-structured algorithms of the SHA-2 family, the US NIST has initiated the SHA-3 contest in order to select a suitable drop-in replacement. In round two of the competition, 14 candidates remain for consideration. Apart from the ongoing cryptanalytic efforts, benchmarking of software and hardware implementations of the candidates will be an important part of the evaluation. Software benchmarking is done for example by NIST on their reference platform and by the eBASH project in the context of the ECRYPT II network of excellence.
In order to complete the hardware analysis of the second round SHA-3 candidates, this thesis implemented six further algorithms, i.e. Blue Midnight Wish, Fugue, Grostl, JH, SHAvite-3,and Skein. The implementations encompass equivalent functionality and interfaces. The design process has been done targeting the UMC 0.18 mm CMOS process technology
This is one of the two chips that implements the functions. The other chip is Roesti. In this chip the functions Blue Midnight Wish and Skein are implemented. See also The SHA3 Hardware Evaluation WWW site.