The IIS Chip Gallery
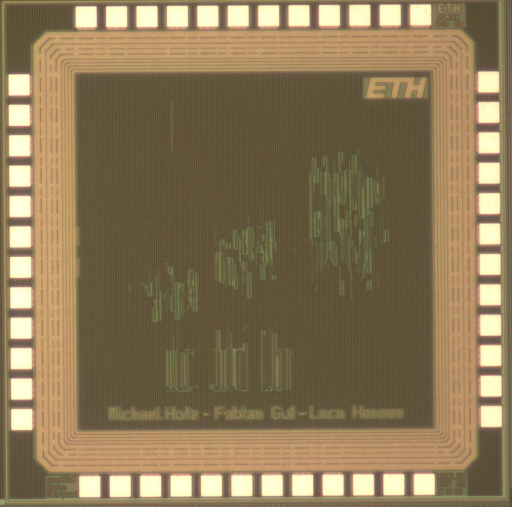
Whirlpool (2008)
by
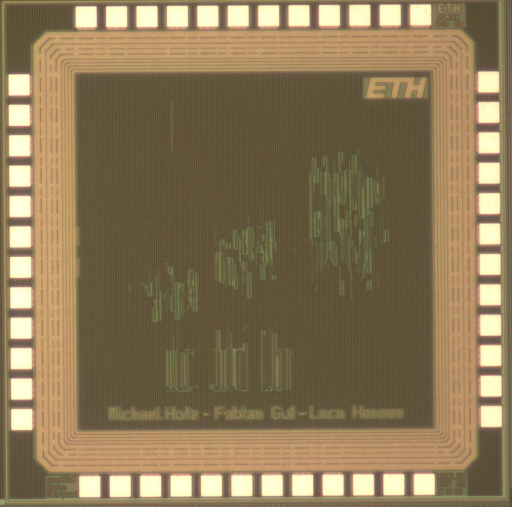
| Application | Cryptography |
| Technology | 180 |
| Manufacturer | UMC |
| Type | Semester Thesis |
| Package | QFN48 |
| Dimensions | 1525μm x 1525μm |
| Gates | 30 kGE |
| Voltage | 1.8 V |
| Power | 18 mW, 1.8V, 200MHz |
| Clock | 200 MHz |
Cryptographic hash functions are ubiquitous algorithms used in numerous schemes like digital signatures, public-key encryption, or MAC\u2019s. Hash functions process an arbitrary-length message to produce a small, fixed-length digital fingerprint. They need to satisfy a variety of security properties (pre-image resistance, collision resistance, pseudo-randomness, etc.).
The SHA-2 hash family was added to the National Institute of Standards and Technology (NIST) Federal Information Processing Standard (FIPS) 180-2 in 2002, in anticipation of the increase in security afforded by the Advanced Encryption Standard (AES) symmetric key algorithm. In February 2003, the Whirlpool hash function was chosen as part of the New European Schemes for Signatures, Integrity and Encryption (NESSIE) initiative, as new advanced cryptographic hash standard.
The main goal of this semester project was to find, evaluate, and develop a low-area/low-power implementation of the Whirlpool hash function. Since Whirlpool, like many new hash algorithms, relies on an AES-based structure, the investigation of a compact solution of its computational core becomes of primal interest for resource-constrained applications. The final lightweight whirlpool design requires only 8.0 kGE and consumes 18 mW at 1.8 V and 200 MHz. The maximal achievable throughput is 62 Mbps