The IIS Chip Gallery
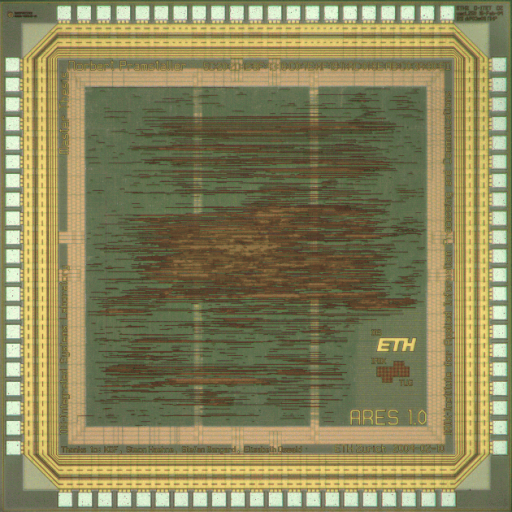
Ares (2004)
by
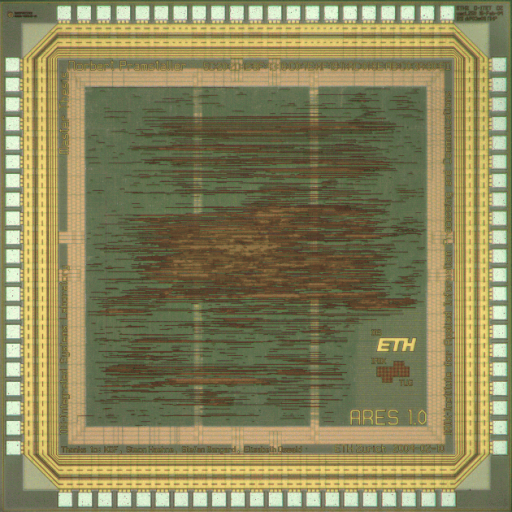
| Application | Cryptography |
| Technology | 250 |
| Manufacturer | UMC |
| Type | Diploma Thesis |
| Package | LCC84 |
| Dimensions | 2500μm x 2500μm |
| Gates | 90 kGE |
| Voltage | 2.5 V |
| Power | 204 mW, 90MHz, 2.5V |
| Clock | 91.7 MHz |
Differential Power Analysis is a very efficient method of attacking hardware implementations of cryptographic algorithms. In such attacks the power consumption of a device implementing the algorithm is observed over many operations. The power consumption of a standard CMOS circuit is dependent on its operators. The attacker makes use of this property and compares the measurement results to a set of pre-computed power curves.
Each power curve is calculated using a simple model of the device and a different key assumption. In a successful attack the power curve generated using the correct portion of the key will exhibit a higher correlation to the measurement result.
In this project a specific family of countermeasures, known as masking methods, have been implemented and evaluated for the Advanced Encryption Standard (AES) algorithm. The masking method prevents direct operations between data and key within the device. The data is masked by a random sequence of numbers prior to any operation involving the key. A specialized parallel computation unit is used to calculate the correct value of the mask so that it can be removed after the operation.
The chip implemented in this project uses two different masking methods, one reported in the literature and the other one developed as part of this project. The implementation occupies roughly the same area of a comparable design (Fastcore), but has a throughput that is around 40% lower.