The IIS Chip Gallery
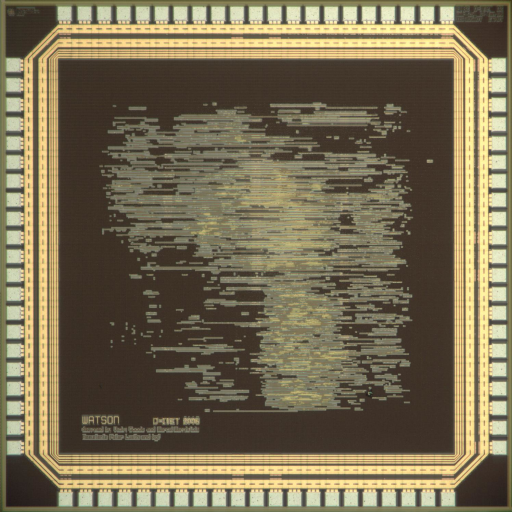
Watson (2006)
by
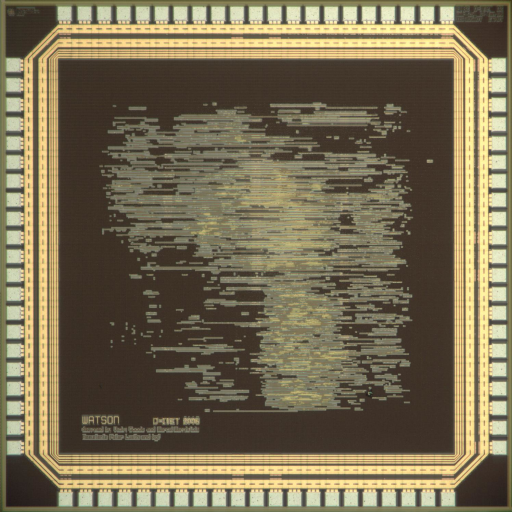
| Application | Cryptography |
| Technology | 250 |
| Manufacturer | UMC |
| Type | Semester Thesis |
| Package | LCC84 |
| Dimensions | 2500μm x 2500μm |
| Voltage | 2.5 V |
| Power | 189-319 mW |
| Clock | 287-400 MHz |
The European Network of Excellence for Cryptography (ECRYPT) has started a multi-year effort called eSTREAM to identify new stream ciphers that might become suitable for widespread adoption. Stream ciphers belong to the class of private key algorithms, where all communication partners have somehow arranged to possess a shared secret key.
Stream ciphers are intended to provide an endless stream of key bits - most probably by using a key of finite length - to encrypt a continuous stream of data, for instance in multimedia applications. The stream of key bits is then XOR?ed with plaintext in order to generate a stream of ciphertext. On the receiving side, an identical stream of key bits is generated using the same cryptographic block. Decryption of the received ciphertext is carried out by XOR?ing the ciphertext once again with the key stream. It is also possible to create stream ciphers by using block ciphers, for instance by feeding back the output of a block cipher to its input.
The attempt of the two IIS student projects dealing with eSTREAM candidates was the implementation and evaluation of hardware performance metrics of up to seven eSTREAM crypto cores. From a total of 34 algorithms submitted to eSTREAM, a subset of 12 were designed with primarily hardware implementations in mind.
A selection of 7 candidates was given to the two student teams, namely Grain, Mickey, Mosquito, Sfinks, Trivium, VEST, and ZK-Crypt. To provide a comparative reference for the implementation results of the stream cipher cores, the well-know Advanced Encryption Standard (AES) block-cipher in output-feedback mode has also been integrated. At the end of the theses, time was left to implement an additional stream cipher candidate, so Achterbahn has been added to the collection. Some cores were integrated multiple times in different architectures.
The stream cipher candidates have been compared in terms of net throughput, total circuit size, time and area required for initialization, energy consumption, and key agility. An other important aspect is the scalability of throughput and circuit area: Mobile, low-rate applications need small and energy-efficient implementations, whereas stationary, high-bandwidth services call for high throughput cores. Since the expertise of the IIS lies in the design of integrated circuits, no statements about the cryptographic security of the underlying algorithms were made. The two stream cipher ASICs - Sherlock and Watson - were integrated in UMC 0.25 mm 1P/5M CMOS technology. Sherlock requires a total core area of 2.91 mm2, Watson occupies a core area of 2.85 mm2.
Detailed results can be found in Hardware evaluation of eSTREAM candidate algorithms page.